[CyberLand News] Weekly #17 - Threats and Malware
Last news on threats, malware and vulnerabilties in the cyber land
Contents
Zero-Day Malware Classification by CrowdStrike
CrowdStrike researchers have developed a method to categorize zero-day malware using machine intelligence and behavioral data. The traditional approach of assigning a family name and attribution to new and unknown malware for categorization is not always accurate and can cause delays in responding to newly discovered threats. CrowdStrike's new method automates the identification of the Threat Type of zero-day malware, allowing for a quicker response to mitigate threats.
Classifying new and unknown malware has always been a challenge in the security industry due to the rapid discovery of new variants. When faced with a new malware instance, questions arise about its nature, the threat it poses, and how to protect against it. The conventional approach involves assigning a family name to the malware and, if possible, attributing it to a threat actor. However, a deeper understanding of the malware's capabilities is needed to fully comprehend the threat it presents to organizations.
CrowdStrike researchers have automated the process of identifying Threat Types, which enables rapid classification of zero-day malware and addresses the challenge of assigning malware family names. Their approach utilizes machine intelligence, behavioral data, pre-defined Threat Type groups, and supervised and unsupervised clustering and similarity assessment. By leveraging these techniques, they can categorize zero-day malware with a measurable degree of confidence, facilitating a quicker response to mitigate threats.
Overall, CrowdStrike's method of categorizing zero-day malware using machine intelligence helps overcome the limitations of manual human analysis and enables more efficient threat mitigation in the face of rapidly evolving threats.
More details in “CrowdStrike Researchers Automate Zero-Day Malware Classification for More Effective Threat Mitigation“
Detection Evasion tactics for Vidar Malware
The threat actors behind the Vidar malware, a commercial information stealer, have made changes to their backend infrastructure in an attempt to conceal their online trail. Cybersecurity company Team Cymru has analyzed these changes and shared their findings. The Vidar malware has been active since late 2018 and is distributed through phishing campaigns, sites offering cracked software, rogue Google Ads, and a malware loader named Bumblebee.
According to Team Cymru's analysis, the Vidar operators have split their infrastructure into two parts: one for regular customers and another for the management team and potentially premium users. The main domain used by the threat actors, my-odin[.]com, has undergone changes as well. Previously, files could be downloaded without authentication, but now users are redirected to a login page. Additionally, the IP address hosting the domain has been updated multiple times, including a shift from 186.2.166[.]15 to 5.252.179[.]201 and then to 5.252.176[.]49. The threat actors have also been observed accessing the latter IP address using VPN servers, potentially to hide their activities within the general internet noise.
Team Cymru detected outbound connections from the 5.252.176[.]49 IP address to a legitimate website called blonk[.]co and a host located in Russia (185.173.93[.]98:443). Furthermore, the Vidar infrastructure introduced a new IP address, 185.229.64[.]137, hosting the my-odin[.]com domain, along with the use of TOR relays by the operators to access their accounts and malware repositories.
These changes to the Vidar malware's backend infrastructure indicate the threat actors' efforts to retool and cover their tracks in response to public disclosures about their operations. Team Cymru's analysis provides insight into the evolution of Vidar's management infrastructure and highlights the steps taken by the threat actors to potentially anonymize their activities.
More details in “Darth Vidar: The Aesir Strike Back“
Additional info in “Darth Vidar: The Dark Side of Evolving Threat Infrastructure“
Abandoned S3 Buckets targeted by supply chain attack
A new type of software supply chain attack targeting open source projects has emerged, involving the hijacking of expired Amazon S3 buckets to serve rogue binaries. In this attack, threat actors take control of abandoned S3 buckets and use them to distribute malware-laden binaries without modifying the actual modules themselves.
The attack was initially discovered in relation to an npm package called bignum. Versions of the package up to 0.13.0 relied on an Amazon S3 bucket to download pre-built binary versions of an addon called node-pre-gyp during installation. However, the binaries were hosted on an expired S3 bucket that had been claimed by a malicious third party. This party now serves malware-containing binaries, which exfiltrate data from users' computers. The attack leverages the fact that even after a bucket is deleted, the pointer to it can continue to exist, allowing the attacker to redirect the pointer to the compromised bucket.
Upon reverse engineering the malware sample, researchers from Checkmarx found that it is capable of stealing user credentials and environment details, transmitting the stolen information to the compromised bucket.
Checkmarx further revealed that numerous packages were found to be using abandoned S3 buckets, making them vulnerable to this novel attack vector. This discovery emphasizes that threat actors are constantly seeking new methods to compromise the software supply chain.
The incident serves as a reminder to developers and organizations about the potential risks associated with abandoned hosting buckets or obsolete subdomains. Even forgotten artifacts can be exploited by malicious actors for data theft and intrusion. It highlights the need for vigilance and proper management of resources in the software supply chain.
This development comes shortly after the discovery by Cyble of 160 malicious Python packages that were estimated to have been downloaded over 45,000 times. These packages had the ability to extract login credentials and credit card details, further underscoring the importance of securing the software supply chain against such threats.
More details in “Hijacking S3 Buckets: New Attack Technique Exploited in the Wild by Supply Chain Attackers“
SSH Servers targeted by Diicot group
Researchers from Cado Labs have discovered a Romanian threat actor group called Diicot that utilizes unique Tactics, Techniques, and Procedures (TTPs) in their attacks. The group employs a brute-force malware with undisclosed payloads that have not been publicly reported or found in common repositories.
Diicot, formerly known as Mexals, is a relatively new group with extensive technical knowledge and diverse objectives. Their recent campaign involves the use of the Cayosin botnet, targeting internet-exposed SSH servers with weak or default credentials. Diicot relies on the Shell Script Compiler to obfuscate loader scripts, and their payloads are packed with a custom version of UPX.
Interestingly, Diicot makes use of Discord for command and control (C2) communication, leveraging HTTP POST requests to a webhook URL. They incorporate Snowflake timestamps in the links for data exfiltration and campaign statistics.
The researchers identified four different channels used by Diicot in this campaign. Additionally, they observed the adoption of the Cayosin botnet, a Mirai-based botnet agent, to target routers running the Linux-based OS OpenWRT, indicating the group's ability to adapt their attack methods.
Diicot's campaigns involve a complex execution chain, where payloads and outputs are interdependent. The group uses the Shc executable as a loader, preparing the system for cryptocurrency mining using a custom version of XMRig. Initial access is gained through a Golang-based 64-bit SSH brute-forcing tool called "aliases," which then launches a Mirai-style spreader script ("bins.sh") to retrieve the Cayosin botnet binaries.
Diicot also engages in doxxing activities and is exploring ways to conduct DDoS attacks. During the examination of their servers, a doxxing video in Romanian language was discovered, revealing a dispute between Diicot and rival hacking group members.
It is important for users to implement SSH hardening measures, such as key-based authentication and firewall rules, to limit access to their systems and prevent exploitation by such threat actors.
More details in “Tracking Diicot: an emerging Romanian threat actor“
Additional info in “How We Tracked a Threat Group Running an Active Cryptojacking Campaign“
UNC3886 exploits VMWare ESXi 0-Day
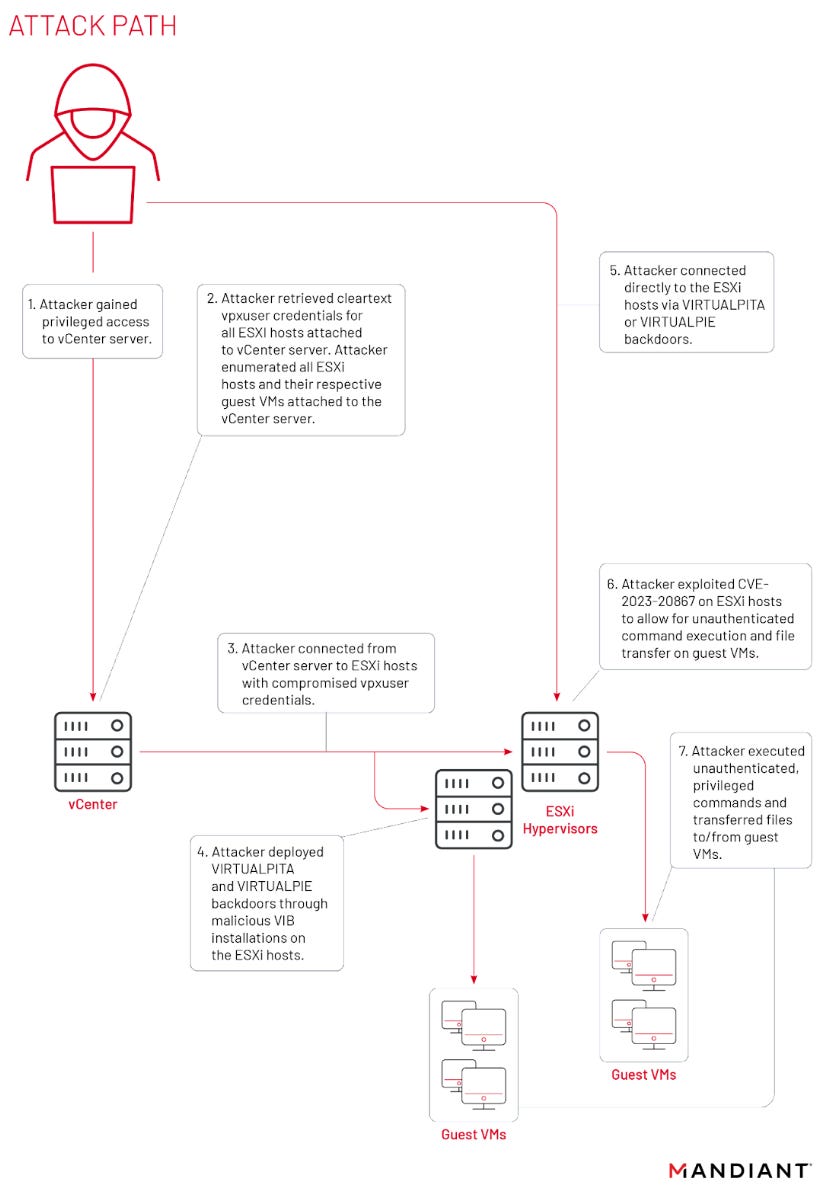
The Chinese cyberespionage group UNC3886 has been observed exploiting a zero-day vulnerability in VMware ESXi to gain escalated privileges on guest virtual machines. The group utilizes malicious vSphere Installation Bundles (VIBs) to install backdoors on ESXi hypervisors, granting them command execution, file manipulation, and reverse shell capabilities. This activity was first reported in September 2022 and primarily affects Windows virtual machines, vCenter servers, and VMware ESXi hosts.
UNC3886 has also leveraged a zero-day vulnerability in VMware Tools to bypass authentication and execute privileged commands on Windows, Linux, and PhotonOS guest virtual machines. The vulnerability, designated as CVE-2023-20867, has been classified as "low severity" as it requires the attacker to have root access to the ESXi server.
The group employs scripts to enumerate ESXi hosts and their guest virtual machines, modify lists of allowed IPs, and collect credentials from compromised vCenter servers. The use of CVE-2023-20867 does not generate authentication log events on the guest virtual machines when commands are executed from the ESXi host.
UNC3886 has also been observed installing two backdoors, VirtualPita and VirtualGate, which utilize VMCI sockets for persistence and lateral movement. These backdoors enable network segmentation bypass, evasion of security inspections for open listening ports, and provide the attackers with a new level of persistence.
The attacks conducted by UNC3886 are highly targeted, with indications of a preference for governmental or government-related targets. The group demonstrates advanced capabilities, including reverse-engineering various parts of the targeted technologies.
Mandiant, the cybersecurity company that reported these findings, notes that UNC3886's use of diverse malware families and specialized tools tailored to the targeted platforms indicates significant research capabilities and an in-depth understanding of the sophisticated technologies they exploit.
UNC3886 is known for targeting organizations involved in defense, technology, and telecommunications in the United States and the Asia-Pacific region, often utilizing zero-day vulnerabilities in firewall and virtualization solutions.
More details in “VMware ESXi Zero-Day Used by Chinese Espionage Actor to Perform Privileged Guest Operations on Compromised Hypervisors“
Additional info in “VMWare Advisory - VMSA-2023-0013“
Additional info in “Fortinet - Analysis of FG-IR-22-369“
ChamelGang - DNS-over-HTTPS for malware comms
The Chinese threat group known as ChamelGang has been found to target Linux devices with a previously unknown malware implant called ChamelDoH. This implant allows for DNS-over-HTTPS (DoH) communication with the attackers' servers, providing an encrypted channel for malicious queries that are difficult to detect.
ChamelGang was initially documented in September 2021, focusing on their Windows toolkit. However, a recent report by Stairwell reveals their expansion into Linux malware. The connection between ChamelGang and the Linux implant is based on a domain previously associated with the threat actor and a custom privilege elevation tool observed in past ChamelGang campaigns.
The use of DoH in ChamelDoH enables encrypted communication between infected devices and the command and control (C2) server, making it challenging to distinguish malicious queries from regular HTTPS traffic. DoH also allows the malware to bypass local DNS servers by leveraging DoH-compatible servers provided by reputable organizations, although this behavior was not observed in this case.
ChamelDoH utilizes two keys stored in its JSON configuration, "ns_record" and "doh," to obtain C2 hostnames and a list of legitimate DoH cloud providers that can be abused for performing DoH queries. The malware's communications are encrypted using AES128 and a modified base64 encoding with substitutes for non-alphanumeric characters. The transmitted data is appended as hostnames to the malware's listed C2 servers.
This modification allows the malware to issue TXT requests for domains containing the encoded C2 communications, obscuring the nature of the requests and reducing the likelihood of detection. The C2 responds with an encoded TXT record containing commands for the malware to execute on the infected device.
ChamelDoH collects basic information about the host, such as the name, IP address, CPU architecture, and system version, and generates a unique ID. It supports various commands that can be remotely issued by the operators via TXT records received in DoH requests, including executing files/shell commands, setting sleep intervals, downloading/uploading files, deleting files, copying files, and changing the working directory.
As of the time of reporting, ChamelDoH is not flagged as malicious by any antivirus engines on VirusTotal, indicating its current ability to evade detection.
Overall, the ChamelGang's use of ChamelDoH highlights their capabilities in targeting Linux devices and utilizing advanced techniques to establish covert and encrypted communication channels with their C2 servers.
More details in “ChamelGang and ChamelDoH: A DNS-over-HTTPS implant“
More details in “Masters of Mimicry: new APT group ChamelGang and its arsenal“
A.I. support for text drafting