[CyberLand News] Weekly #18 - Threats and Malware
Last news on threats, malware and vulnerabilties in the cyber land
Contents
Threat for NPM - Manifest confusion attack
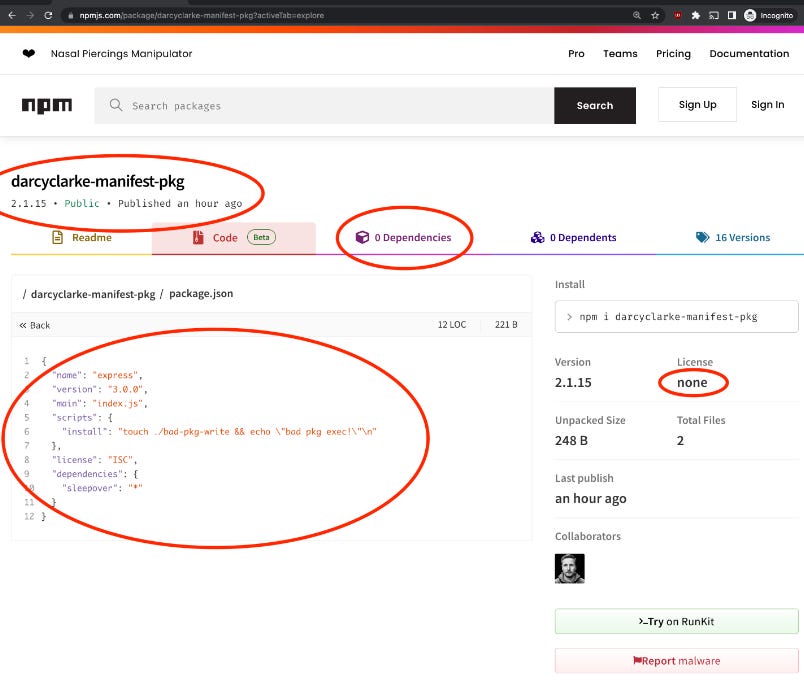
The security vulnerability known as "manifest confusion" poses a significant threat to the NPM (Node Package Manager) registry, compromising the integrity of packages and enabling attackers to hide malware or execute malicious scripts during installation.
NPM, the default package manager for Node.js, is widely utilized by developers worldwide, facilitating the automated installation, upgrade, and configuration of software packages from the npmjs.com registry.
Despite knowledge of the issue since November 2022, little has been done to address the risks associated with manifest confusion, as highlighted by former GitHub and npm engineer Darcy Clarke.
The popularity of the NPM registry makes it an attractive target for threat actors seeking to distribute malicious packages, potentially compromising users' computers, stealing credentials, or deploying ransomware.
Manifest confusion occurs when there is a mismatch between a package's manifest information on the npm registry and its 'package.json' file, leading to inconsistencies in the data. Threat actors can manipulate the manifest data to hide dependencies and scripts from the registry, while they still exist in the package.json and are executed during installation.
This inconsistency poses various risks, including cache poisoning, installation of unknown dependencies, execution of unknown scripts, and potential downgrade attacks.
Furthermore, hidden install scripts and dependencies can be included, evading detection by most security tools and the npm website. This problem affects the npm community and major package managers, eroding trust in the accuracy of dependencies and version numbers.
To mitigate the issue, developers should manually review the package.json to verify version numbers, dependencies, and executed scripts. However, this problem persists due to the size of npm and the long-standing nature of the issue.
Clarke recommends that package authors and maintainers rely less on manifest data and source metadata, excluding name and version, directly from package.json files, which are less susceptible to manipulation. Another preventive measure involves using a registry proxy to implement additional checks and ensure consistency between manifest data and package information.
GitHub, which acquired npm in 2020, has been aware of this problem but has not yet resolved it or communicated the risks to the npm community. Efforts to address manifest confusion and enhance security in the npm ecosystem are crucial to protect developers and users from potential cyber threats.
More details in “The massive bug at the heart of the npm ecosystem“
Additional info in “Manifest Confusion: How Socket Protects You“
Additional info in “npm packages caught serving TurkoRAT binaries that mimic NodeJS“
Additional info in “npm packages caught serving TurkoRAT binaries that mimic NodeJS“
Additional info in “Popular 'coa' NPM library hijacked to steal user passwords“
MITRE - Top25 Common Weakness Enumeration (CWE)
MITRE has released its list of the top 25 most dangerous weaknesses in software over the past two years. These weaknesses encompass various issues, such as flaws, bugs, vulnerabilities, and errors in software code, architecture, implementation, or design.
The identified weaknesses pose serious threats to the security of systems running the affected software. They can serve as entry points for malicious actors aiming to gain control, access sensitive data, or cause denial-of-service incidents.
MITRE's list was created by scoring each weakness based on severity and prevalence. The analysis considered nearly 44,000 CVE entries from the National Vulnerability Database (NVD) and focused on vulnerabilities documented in CISA's Known Exploited Vulnerabilities (KEV) catalog.
The identified weaknesses are highly impactful and have been widely observed in software released in the past two years. Exploitation can lead to complete control of systems, data exfiltration, or denial-of-service attacks.
Sharing this list allows the broader community to prioritize addressing these critical software security weaknesses. It complements collaborative efforts by cybersecurity authorities, such as the joint release of the top 15 commonly exploited vulnerabilities in 2021 and the inventory of exploited bugs in 2020.
CISA encourages developers and security response teams to review the CWE Top 25 and consider adopting recommended mitigations. MITRE will also provide further articles on methodology, vulnerability trends, and the importance of vulnerability management in mitigating cybersecurity risks.
More details in “2023 “CWE Top 25”“
More details in “2023 CWE Top 25 Most Dangerous Software Weaknesses“
More details in “2023 CWE Top 25 Key Insights“
Additional info in “CISA - Known Exploited Vulnerabilities Catalog“
Additional info in “CISA - Top Routinely Exploited Vulnerabilities“
Akira ransomware targets VMWare ESXi
The Akira ransomware operation has expanded its targeting to include VMware ESXi virtual machines in double-extortion attacks against companies globally. Initially focused on Windows systems in various industries, Akira has now incorporated a Linux encryptor specifically designed to target VMware ESXi servers.
By encrypting ESXi servers, the threat actors can impact multiple virtual machines in a single attack, considering the widespread adoption of virtual machines in enterprise environments. While Akira's Linux encryptor lacks advanced features seen in other VMware ESXi encryptors, it does offer customization options through command line arguments.
Notably, the encryptor allows attackers to define the encryption percentage per file, influencing the encryption speed and the likelihood of victims recovering their files without paying a ransom.
The Linux variant of Akira skips certain Windows-related folders and files, suggesting that it may have been ported from the Windows version of the ransomware. Cyble's analysts have reported that the Linux encryptor employs multiple symmetric key algorithms, such as AES, CAMELLIA, IDEA-CB, and DES, along with a public RSA encryption key.
Encrypted files are renamed with the .akira extension, and a ransom note named akira_readme.txt is created in each encrypted folder. The ransomware operation has already targeted over 30 victims in the United States alone, and recent activity spikes indicate ongoing attacks.
Akira's inclusion of Linux support follows a trend among ransomware groups, which find it profitable to expand their reach. Other ransomware operations utilizing Linux encryptors, often targeting VMware ESXi, include Royal, Black Basta, LockBit, BlackMatter, AvosLocker, REvil, HelloKitty, RansomEXX, and Hive.
This development underscores the increasing need for organizations to enhance their security measures to mitigate the evolving threat landscape posed by ransomware attacks.
More details in “Cyble - Akira Ransomware Extends Reach to Linux Platform“
Andariel group uses EarlyRAT malware
Security analysts have discovered a previously undisclosed remote access trojan (RAT) called "EarlyRAT," which is used by Andariel, a sub-group of the Lazarus North Korean state-sponsored hacking group. Andariel, also known as Stonefly, is associated with Lazarus, a hacking group known for using the DTrack modular backdoor to gather information from compromised systems.
WithSecure recently reported that a North Korean group, potentially Andariel, had collected valuable intellectual property over a two-month period using a newer variant of DTrack. Andariel has also been linked to Maui ransomware deployments in Russia, India, and Southeast Asia, suggesting a focus on generating revenue.
Andariel employs EarlyRAT to collect system information from compromised devices and send it to the attacker's command and control (C2) server. The discovery of EarlyRAT by Kaspersky contributes to understanding the group's tactics and helps defenders detect and prevent associated intrusions.
Kaspersky found EarlyRAT while investigating an Andariel campaign that targeted corporate networks using the Log4Shell vulnerability in mid-2022. Andariel leveraged off-the-shelf tools like 3Proxy, Putty, Dumpert, and Powerline for network reconnaissance, credential theft, and lateral movement.
Phishing documents with macros were observed in these attacks, fetching an EarlyRAT payload from a server associated with past Maui ransomware campaigns.
EarlyRAT is a simple tool that, upon execution, gathers system information and sends it to the C2 server via a POST request. Its secondary function is to execute commands on the compromised system, potentially downloading additional payloads, exfiltrating data, or disrupting operations.
Kaspersky notes that EarlyRAT bears similarities to MagicRAT, another Lazarus tool that can create scheduled tasks and download additional malware from the C2.
Researchers suggest that the observed activities of EarlyRAT were conducted by an inexperienced human operator, as evidenced by the number of mistakes and typos. Manual typing of various commands on compromised network devices often led to errors caused by typos.
Similar operator mistakes were previously uncovered by WithSecure's analysts, who observed a Lazarus campaign where an operator forgot to use a proxy, inadvertently exposing their North Korean IP address at the start of their workday.
More details in “Andariel’s silly mistakes and a new malware family“
Additional info in “Andariel evolves to target South Korea with ransomware“
ThirdEye - A new InfoStealer in the land
FortiGuard Labs recently discovered a malicious infostealer called "ThirdEye" during a routine review of suspicious files. Although not highly sophisticated, this malware is designed to gather various pieces of data from infected devices, which can be used as a foundation for future attacks.
The investigation began when researchers at FortiGuard Labs encountered an archive file named "Табель учета рабочего времени.zip" (translated as "time sheet"). Upon further examination, they identified two files within the archive that were confirmed to be malicious.
Both files have a double extension, with ".exe" followed by a different document-related extension. One of the files is named "CMK равила oормлени олнин листов.pdf.exe" and is labeled "QMS Rules for issuing sick leave" in English. The SHA2 hash value of this file is "f6e6d44137cb5fcee20bcde0a162768dadbb84a09cc680732d9e23ccd2e79494."
The ThirdEye infostealer exhibits relatively simple functionality. It collects various system information from compromised machines, including BIOS and hardware data, ongoing processes, folders and files, and network data. Once the malware is executed, it sends this gathered information to its command-and-control (C2) server, located at "hxxp://shlalala[.]ru/general/ch3ckState." Unlike other infostealers, ThirdEye does not perform any additional actions.
One unique string sequence associated with the ThirdEye infostealer family is "3rd_eye," which is decrypted and combined with another hash value to identify the malware to the C2 server.
The second file in the archive, "Табель учета рабочего времени.xls.exe," shares the same name as its parent file. This file is a variant of the ThirdEye infostealer and serves the same purpose as "f6e6d44137cb5fcee20bcde0a162768dadbb84a09cc680732d9e23ccd2e79494."
Although there is no concrete evidence confirming that ThirdEye has been used in actual attacks, the malware is designed to steal valuable information from compromised machines, allowing threat actors to gain a better understanding of potential targets and potentially narrowing them down further. It is also speculated that victims of this infostealer may become targets of future cyberattacks.
While ThirdEye is not currently considered a severe threat, FortiGuard's investigation suggests that the threat actors behind it are actively enhancing the infostealer. Recent samples of ThirdEye have been found to collect more system information compared to older variants, indicating potential further improvements in the future.
More details in “New Fast-Developing ThirdEye Infostealer Pries Open System Information“
Additional info in “VT analysis“
Detect Cobalt Strike Beacon and Team server
Researchers from Unit 42 have recently discovered two instances of Cobalt Strike Team Server hosted on the internet, along with new profiles that are not publicly available. The aim of their investigation is to shed light on the specific techniques employed by attackers to exploit the Cobalt Strike platform and evade signature-based detection methods.
The identified Team Server instances were found to be connected to the internet and serving as hosts for Beacon implants, providing command-and-control (C2) functionality. To gain a deeper understanding of the evasion techniques used, the researchers extracted the Malleable C2 profile configuration from the Beacon binary.
The operators behind these Cobalt Strike Team Servers made efforts to conceal their C2 infrastructure by leveraging benign and widely recognized services, with the intention of evading detection. Additionally, the researchers found instances of Team Server C2 infrastructure hosted on well-known public cloud infrastructure providers. Furthermore, the operators deployed new Malleable C2 profiles, which are customized configurations used to deceive security controls, bypass security measures, and avoid detection. These profiles involve modifications to HTTP URLs, header parameters, and host headers using harmless and widely recognized domains.
By analyzing these instances and profiles, the researchers aim to provide insights into the evasion techniques used by threat actors and red team actors alike. This knowledge can be valuable in enhancing security controls and developing effective detection and mitigation strategies against Cobalt Strike-based attacks.
More details in “Detecting Popular Cobalt Strike Malleable C2 Profile Techniques“
A.I. support for text drafting